0.将Android sparse image格式转换为raw image
simg2img super.img super.img.raw
1.提取 system分区
有两个工具,一个是Android项目中的 lpunpack, 另一个大神的imjtool
lpunpack --partition=system super.img.raw lpunpack --partition=vendor super.img.raw lpunpack --partition=product super.img.raw 提取所有 lpunpack super.img.raw
imgtool的命令为
./imjtool.ELF64 super.img.raw extract MMapped: 0x7f460c400000, imgMeta 0x7f460c401000 liblp dynamic partition (super.img) - Blocksize 0x1000, 3 slots LP MD Header @0x3000, version 10.2, with 10 logical partitions on block device of 8704 GB, at partition super, first sector: 0x800 Partitions @0x3100 in 3 groups: Group 0: default Group 1: qti_dynamic_partitions_a Name: odm_a (read-only, Linux Ext2/3/4/? Filesystem Image, @0x100000 spanning 1 extents of 1 MB) - extracted Name: product_a (read-only, Linux Ext2/3/4/? Filesystem Image, @0x300000 spanning 1 extents of 474 MB) - extracted Name: system_a (read-only, Linux Ext2/3/4/? Filesystem Image, @0x1de00000 spanning 1 extents of 5 GB) - extracted Name: system_ext_a (read-only, Linux Ext2/3/4/? Filesystem Image, @0x15f600000 spanning 1 extents of 473 MB) - extracted Name: vendor_a (read-only, Linux Ext2/3/4/? Filesystem Image, @0x17d000000 spanning 1 extents of 2 GB) - extracted Group 2: qti_dynamic_partitions_b Name: odm_b (read-only, empty) - extracted Name: product_b (read-only, empty) - extracted Name: system_b (read-only, empty) - extracted Name: system_ext_b (read-only, empty) - extracted Name: vendor_b (read-only, empty) - extracted 如果遇到错误,请用sudo执行
2. 修改system.img为可写
fallocate -l 2G system.img /sbin/resize2fs system.img 2G
看实际的system.img的大小,适当大一些
6G
3.0 移除共享块
如果报错 couldn’t mount RDWR because of unsupported optional features (4000)
4000特性就是 EXT4_FEATURE_RO_COMPAT_SHARED_BLOCKS
可以用下面的命令 去掉
e2fsck -y -E unshare_blocks system.img
也可以检查是否有这个feature
/sbin/dumpe2fs vendor_a.img ... Filesystem features: ext_attr dir_index .... extra_isize shared_blocks
3.1 挂载
mount -t ext4 -o loop system.img system 如果是EROFS 只读文件系统 mount -t erofs -o loop system.ext4.img /mnt
4. 编辑 system目录下的文件
...
5. 卸载 system 目录
umount system
6.修改文件系统错误
e2fsck -yf system.img
7. 让system.img占用尽可能小的空间
resize2fs -M system.img e2fsck -yf system.img
8. 查看真实分区大小
stat -c '%n %s' system.img stat -c '%n %s' * product.img 1596944384 system.img 1128718336 vendor.img 544976896
8.写回
lpmake --metadata-size 65536 --super-name super --metadata-slots 1 --device super:4294967296 --group main:3139354624 --partition system:readonly:1128718336:main --image system=./system.img --partition vendor:readonly:544976896:main --image vendor=./vendor.img --partition product:readonly:1596944384:main --image product=./product.img --sparse --output ./super.new.img group这里是所有分区的文件大小加起来的和
–metadata-slots 要跟 imjtool 工具输出的一样
实际, device-size设置为8G
lpmake --metadata-size 65536 --device-size=8589934592 --metadata-slots=3 --group=qti_dynamic_partitions_a:8053952512 --partition=odm_a:none:1470464:qti_dynamic_partitions_a --partition=product_a:none:407822336:qti_dynamic_partitions_a --partition=system_a:none:4835311616:qti_dynamic_partitions_a --partition=system_ext_a:none:496226304:qti_dynamic_partitions_a --partition=vendor_a:none:2313121792:qti_dynamic_partitions_a --image=odm_a=./odm_a.img --image=product_a=./product_a.img --image=system_a=./system_a.img --image=system_ext_a=./system_ext_a.img --image=vendor_a=./vendor_a.img --group=qti_dynamic_partitions_b:0 --partition=odm_b:none:0:qti_dynamic_partitions_b --partition=product_b:none:0:qti_dynamic_partitions_b --partition=system_b:none:0:qti_dynamic_partitions_b --partition=system_ext_b:none:0:qti_dynamic_partitions_b --partition=vendor_b:none:0:qti_dynamic_partitions_b --image=odm_b=./odm_b.img --image=product_b=./product_b.img --image=system_b=./system_b.img --image=system_ext_b=./system_ext_b.img --image=vendor_b=./vendor_b.img --sparse --output /media/3/tmp/super.new.img lpmake I 10-14 19:06:49 11155 11155 builder.cpp:1031] [liblp]Partition odm_a will resize from 0 bytes to 1470464 bytes lpmake I 10-14 19:06:49 11155 11155 builder.cpp:1031] [liblp]Partition product_a will resize from 0 bytes to 407822336 bytes lpmake I 10-14 19:06:49 11155 11155 builder.cpp:1031] [liblp]Partition system_a will resize from 0 bytes to 4835311616 bytes lpmake I 10-14 19:06:49 11155 11155 builder.cpp:1031] [liblp]Partition system_ext_a will resize from 0 bytes to 496226304 bytes lpmake I 10-14 19:06:49 11155 11155 builder.cpp:1031] [liblp]Partition vendor_a will resize from 0 bytes to 2313121792 bytes Invalid sparse file format at header magic Invalid sparse file format at header magic Invalid sparse file format at header magic Invalid sparse file format at header magic Invalid sparse file format at header magic Invalid sparse file format at header Invalid sparse file format at header Invalid sparse file format at header Invalid sparse file format at header Invalid sparse file format at header
lpmake --metadata-size 65536\ --device-size=4294967296\ --metadata-slots=3\ --group=google_system_dynamic_partitions_a:2222931968\ --partition=odm_a:none:700416:google_system_dynamic_partitions_a\ --partition=product_a:none:266579968:google_system_dynamic_partitions_a\ --partition=system_a:none:1363767296:google_system_dynamic_partitions_a\ --partition=system_ext_a:none:359391232:google_system_dynamic_partitions_a\ --partition=vendor_a:none:232493056:google_system_dynamic_partitions_a\ --image=odm_a=./odm_a.img\ --image=product_a=./product_a.img\ --image=system_a=./system_a.img\ --image=system_ext_a=./system_ext_a.img\ --image=vendor_a=./vendor_a.img\ --group=google_system_dynamic_partitions_b:24563712\ --partition=odm_b:none:0:google_system_dynamic_partitions_b\ --partition=product_b:none:0:google_system_dynamic_partitions_b\ --partition=system_b:none:24563712:google_system_dynamic_partitions_b\ --partition=system_ext_b:none:0:google_system_dynamic_partitions_b\ --partition=vendor_b:none:0:google_system_dynamic_partitions_b\ --image=odm_b=./odm_b.img\ --image=product_b=./product_b.img\ --image=system_b=./system_b.img\ --image=system_ext_b=./system_ext_b.img\ --image=vendor_b=./vendor_b.img\ --sparse \ --output ./super.new.img
参考资料:
https://forum.xda-developers.com/t/editing-system-img-inside-super-img-and-flashing-our-modifications.4196625/
https://blog.senyuuri.info/posts/2022-04-27-patching-android-super-images/
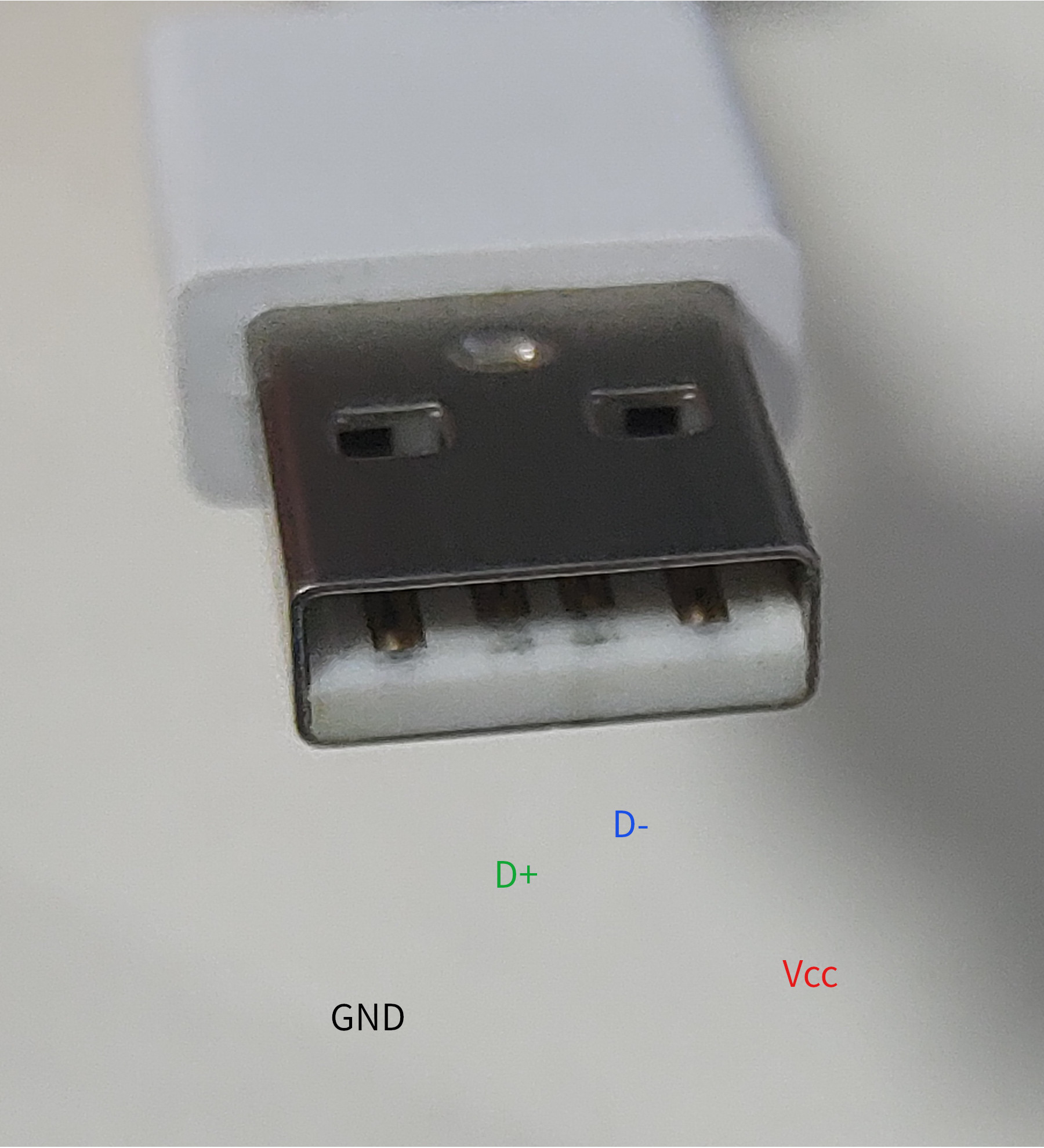 Type A 公头 引脚定义
Type A 公头 引脚定义